REVERSE_ENGINEERING // THREAT_INTELLIGENCE_REPORTING // ATTACK_CHAIN_MAPPING // SYSTEM_VALIDATION // FORENSIC_ANALYSIS // TECHNICAL_INTELLIGENCE // SYS-STATE: ACTIVE_ARCHIVE // OPERATIONAL_RESILIENCE
REVERSE_ENGINEERING // THREAT_INTELLIGENCE_REPORTING // ATTACK_CHAIN_MAPPING // SYSTEM_VALIDATION // FORENSIC_ANALYSIS // TECHNICAL_INTELLIGENCE // SYS-STATE: ACTIVE_ARCHIVE // OPERATIONAL_RESILIENCE
| OPERATIONAL_RECORDS: CASE STUDIES
Documented
Interventions.
Case studies detailing technical execution across sovereign infrastructure, regulated financial environments, and high-trust digital platforms. Each record captures the conditions, constraints, and engineering decisions that shaped the outcome.


Cloud-Native Legal Practice Management Platform for the MENA Region

Security Validation: National 5G Router Deployment.
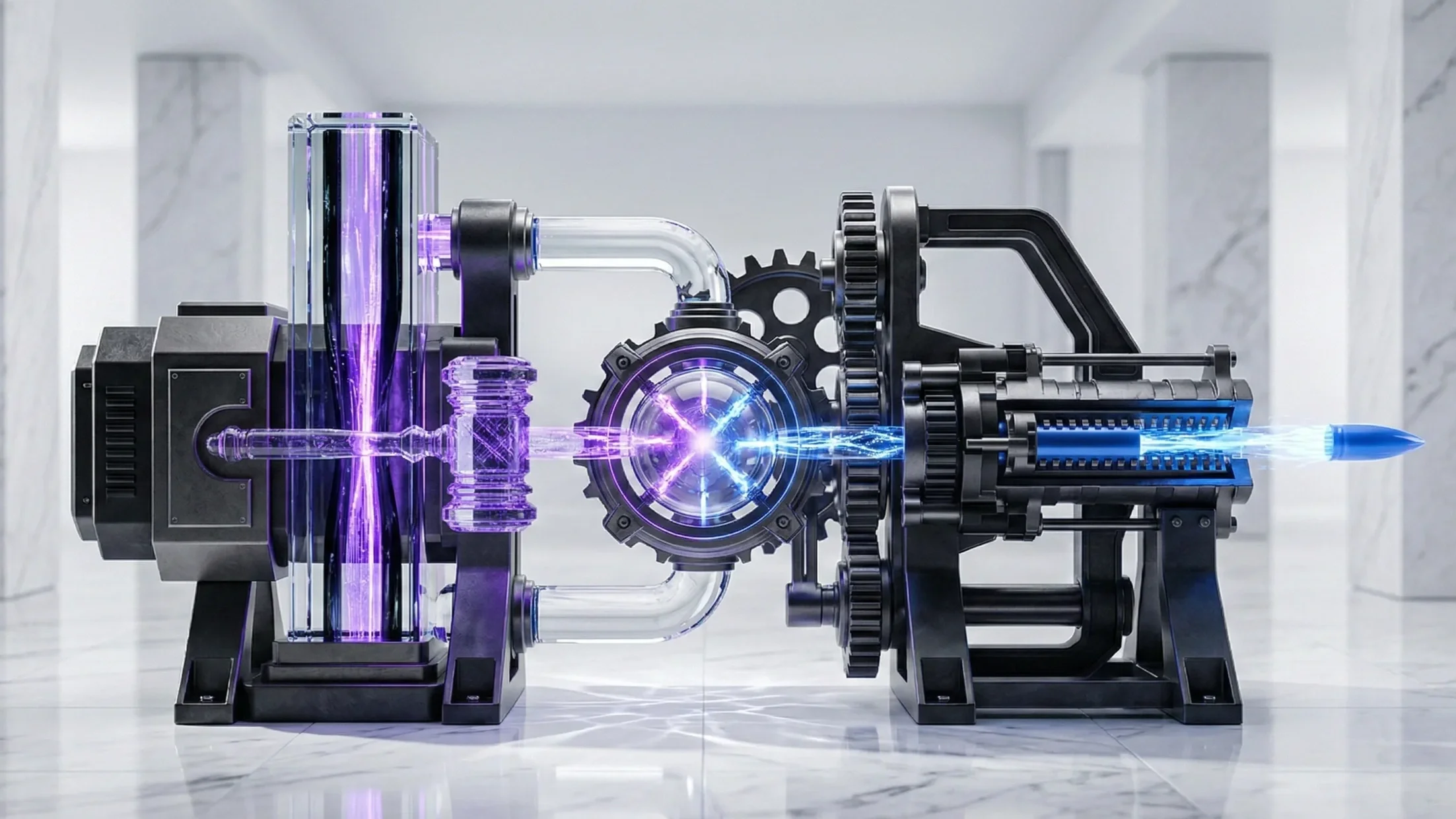
IT/OT Security Assessment for a Critical Gulf Energy Facility
Greenfield Digital Asset Bank Architecture.
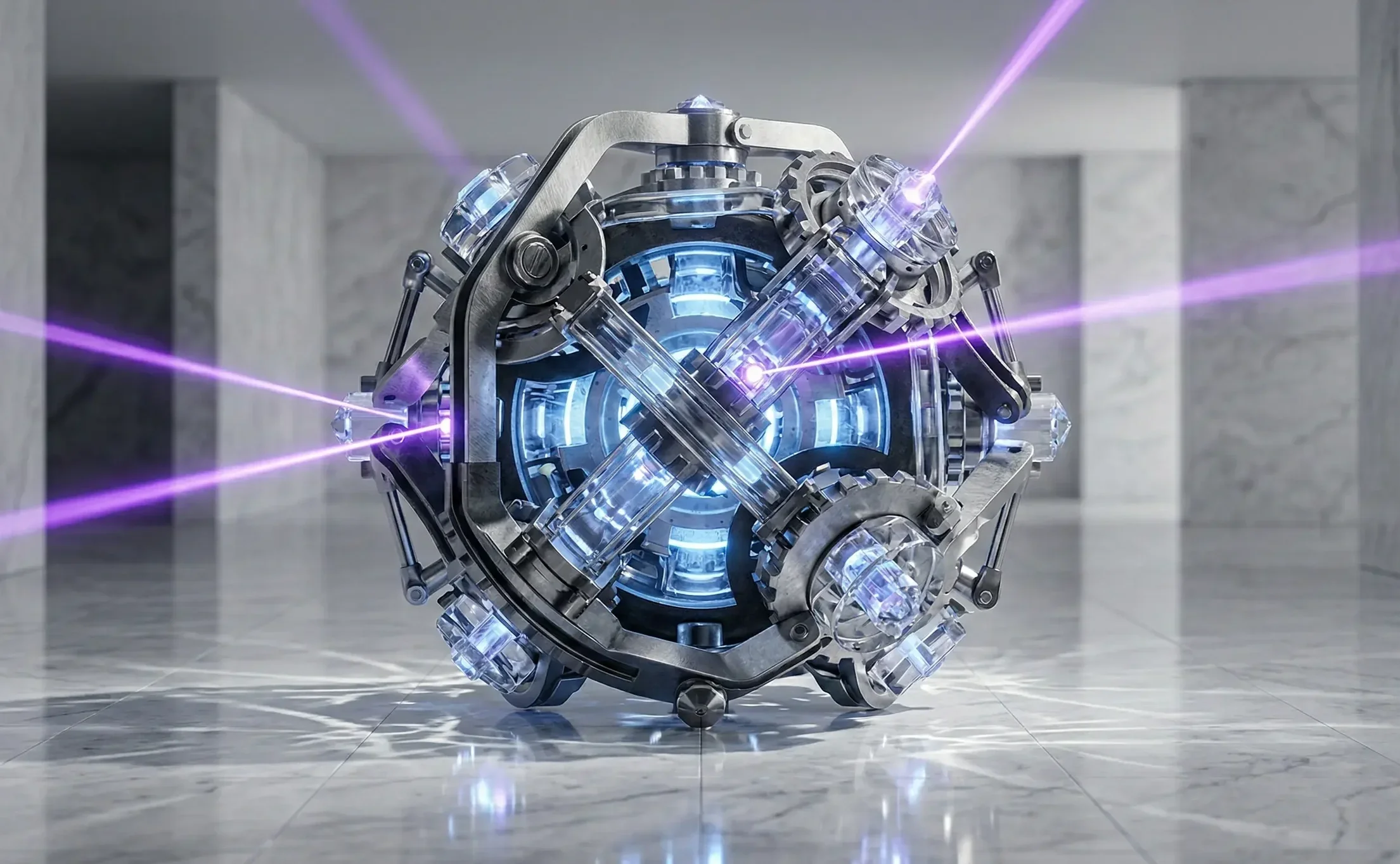
Reverse Engineering Stuxnet — The First Industrial Cyber Weapon.
ICS/SCADA Security Assessment for a Major International Airport

Fault-Tolerant PoS Validator Infrastructure

Incident Response for a Compromised Government Executive Office
Engineering a Regulated Crypto Derivatives Exchange (SEF)

