SYS-STATE: SOVEREIGN RESILIENCE // CONTROL-PLANE INTEGRITY // ADVERSARIAL VALIDATION // GOVERNANCE DEFENSIBILITY // CONTINUITY OF AUTHORITY // FAULT-TOLERANT ARCHITECTURE // INFRASTRUCTURE HARDENING // THREAT MODELING // MISSION-CRITICAL ENGINEERING //
SYS-STATE: SOVEREIGN RESILIENCE // CONTROL-PLANE INTEGRITY // ADVERSARIAL VALIDATION // GOVERNANCE DEFENSIBILITY // CONTINUITY OF AUTHORITY // FAULT-TOLERANT ARCHITECTURE // INFRASTRUCTURE HARDENING // THREAT MODELING // MISSION-CRITICAL ENGINEERING //
| Sector: Digital Asset Institutions
Regulated
Finality.
Lucenor engineers environments where custody integrity, transaction finality, and control-plane correctness are mandatory. We execute structural interventions for custodians, regulated exchanges, tokenization platforms, and institutional brokerages.
// Module 02: Constraints
What matters here
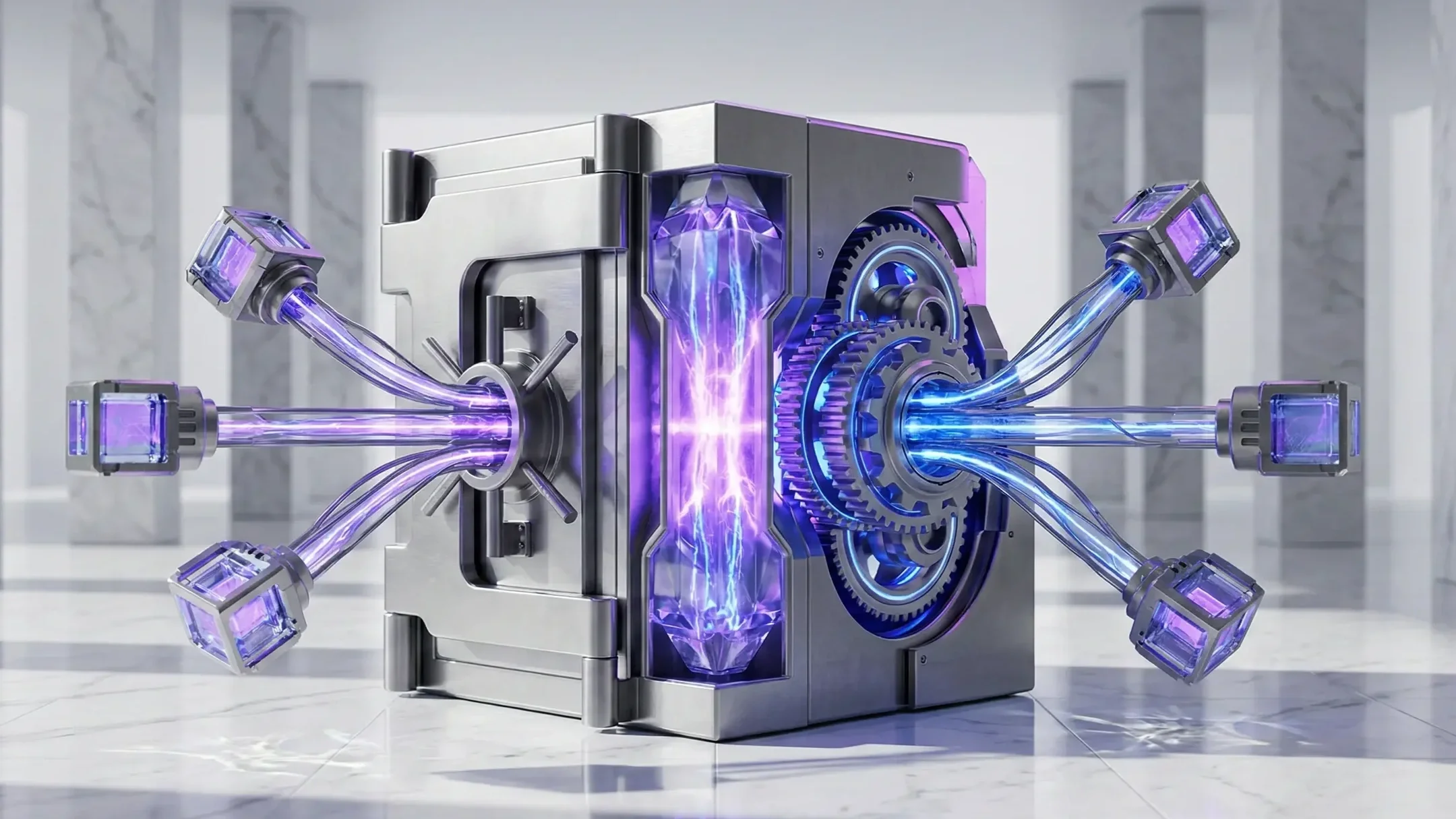
Custody and settlement are control-plane problems. Architecture must output finality, integrity, and regulatory defensibility under multi-jurisdiction scrutiny
STATE: ACTIVE
FAULT-TOLERANCE: BYZANTINE
[01]
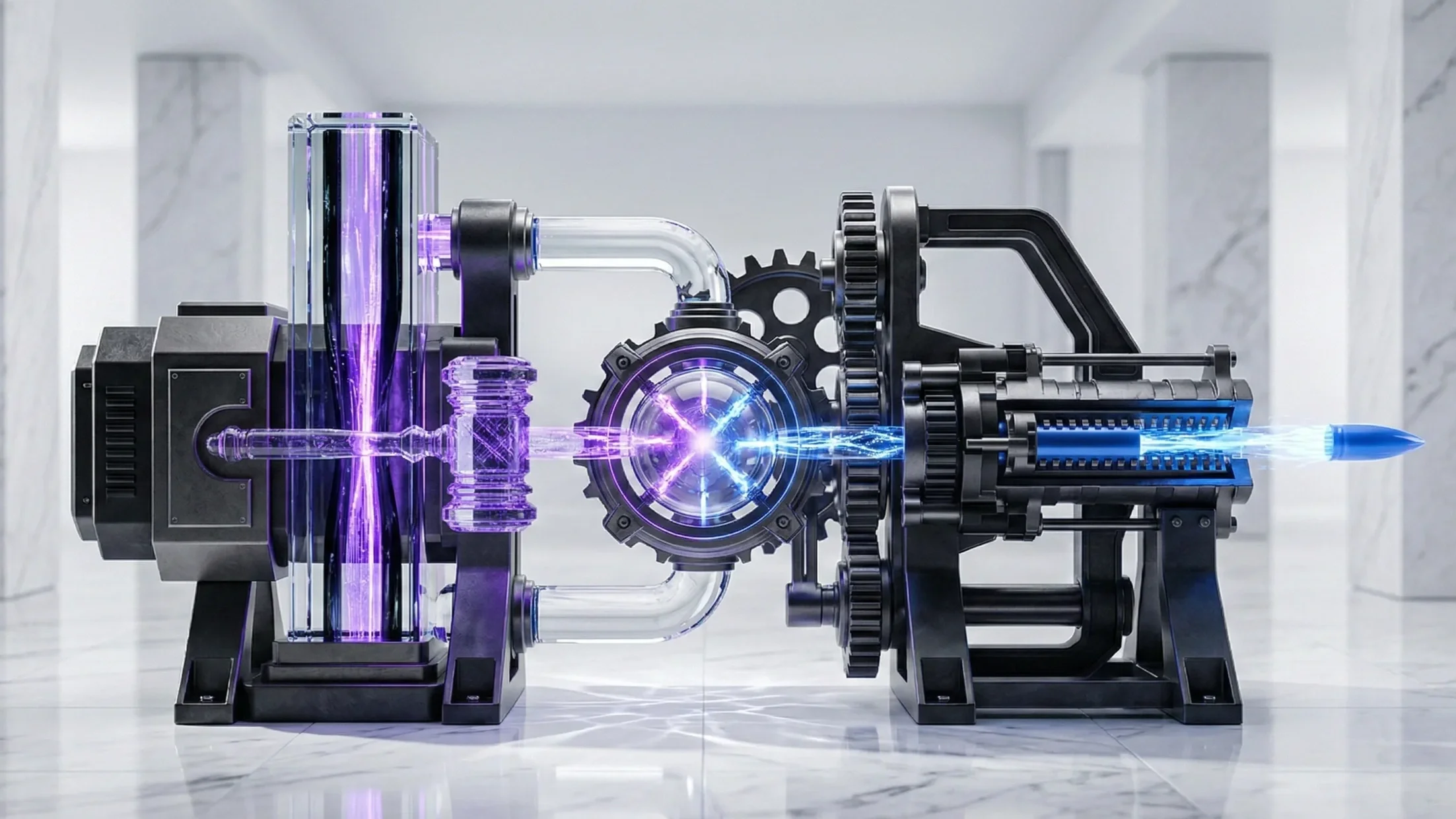
Fault-tolerant architectures designed to remain stable under advanced threat pressure and partial-failure states
Sovereign Resilience
STATE: ACTIVE
EVIDENCE: CRYPTOGRAPHIC
[02]
Architectures engineered to be defensible under frameworks such as ADGM, CFTC, and SPDI-class regimes
Regulatory Compliance
STATE: ACTIVE
DEPLOYMENT: AIR-GAPPED
[03]
Day-Zero Build
End-to-end engineering of minting flows, MPC/HSM custody, and exchange infrastructure
[ PIPELINE: ACTIVE ]
SEQ: 01-04
// Module 03: Interventions
Operating context
-
Engineering of MPC and HSM controls, minting/burn authorization, and bank-grade settlement ledgers. Securing the transaction lifecycle at the cryptographic layer.
-
Design of multi-region, active-active infrastructure with deterministic reconciliation mechanics. Failure-domain containment and recovery sequencing for critical service planes.
-
Formal verification and audits for high-value DeFi/CeFi bridges and on-chain control surfaces. Threat-informed acceptance criteria for contract upgrades and admin keys.
-
Adversarial simulation derived from offensive tradecraft to validate threat models against realistic attacker capability. Control-plane exposure reduction through strict pathway governance.
// Module 04: Ledger
Primary case studies
[ DOC-01 ] Blockchain Infrastructure
[ DOC-02 ] FinTech Engineering
[ Index format ]
Sys-Def: Active
[ DOC-02 ] Digital Finance Architecture
// Module 05: System access
Initiate an engineering review.
We evaluate cryptographic custody boundaries, validate settlement finality, and engineer regulated infrastructure built to withstand adversarial pressure.
SECURE_CHANNEL: OPEN
AWAITING_INPUT_
Institutional Identity